DATA ACCESS GOVERNANCE SOLUTION
Protect and Control Your Data with Qlik's Data Access Governance Solution
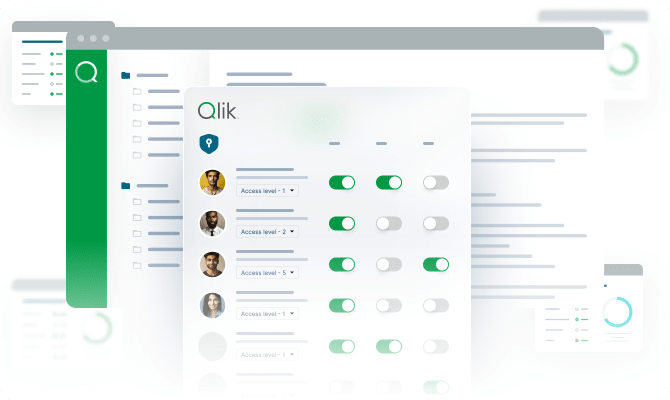
Control and protect your data with comprehensive access governance. Manage permissions, enforce policies, and ensure compliance across your data ecosystem with centralized security.

How Qlik's Data Access Governance Solution works
Step 1 - Discover and classify sensitive and regulated data
Step 2 - Define user roles, access levels, and data policies
Step 3 - Automate policy enforcement and permission updates
Step 4 - Audit and monitor data usage across the enterprise

Why choose Qlik for data access governance
One platform for all access governance needs
Simplify security administration with centralized platform that manages permissions, policies, and access controls across all data assets from a single interface.

Governance that extends everywhere
Apply consistent access controls across Qlik platforms and external systems including data warehouses, lakes, and applications through native integrations and standard protocols.

Meet regulatory requirements automatically
Support GDPR, HIPAA, SOC 2, and other regulatory requirements with automated controls, audit trails, and privacy protections that demonstrate compliance during audits.

Governance that business users understand
Enable data stewards to define business-oriented access policies through intuitive interfaces while IT maintains technical controls and security enforcement mechanisms.

Enterprise-proven security and governance
Join organizations that protect sensitive customer, financial, and operational data with Qlik's governance, ensuring security without sacrificing analytics accessibility.
Trusted by leading enterprises worldwide
What our customers say
Connect to 500+ data sources with Qlik’s analytics integrations
Resources
Data Access Governance Solution FAQs
Policies define access rules using business logic that automatically determines permissions based on context, eliminating manual administration and ensuring consistent security enforcement.
Yes, context-aware policies evaluate user attributes, data sensitivity, time, location, and other factors dynamically to grant appropriate access for each request.
Temporary access grants, partner-specific policies, and data masking enable controlled sharing with external users while protecting sensitive information and maintaining audit visibility.
Automated workflows detect role changes, update permissions accordingly, and notify administrators while ensuring users maintain necessary access during transitions.



























































































